Smart Home Security Research - CVE-2025-14300 Assigned
- CRAC Learning

- Apr 7
- 2 min read
Updated: Apr 14

The CRAC Learning team is back with another CVE as part of the Smart Home Security Research Program. An unauthenticated configuration issue in the connectAP API of the TP-Link Tapo C100 v5 IP camera. The bug allows a local attacker on the same network segment to submit unauthorized Wi-Fi reconfiguration requests to the device, forcing the camera to connect to an attacker-controlled network and causing service denial, stream loss, and a broader confidentiality impact. TP-Link assigned us this issue CVE-2025-14300 and rated it as High severity bug with CVSS v4.0 8.7. The weakness maps to CWE-306: Missing Authentication for Critical Function.
The vulnerable functionality is in the camera’s HTTPS management interface via a connectAP endpoint. This endpoint accepts JSON parameters describing the target including SSID, BSSID, password, and encryption metadata. The problem is not present in the API itself, but the absence of any authentication or authorization before accessing it. As a result, any attacker present in the LAN can send a crafted request and force the camera to connect to an attacker controller network without authenticating.
From an attacker's perspective, a critical operation is reachable over the network, yet it fails to strictly enforce any session binding, token validation, or any other equivalent method to prove who you are. Because the endpoint accepts configuration data that can change it's wifi state, exploitation is not only limited to a DoS attack. It can even break legitimate access to the camera’s live video and audio streams.
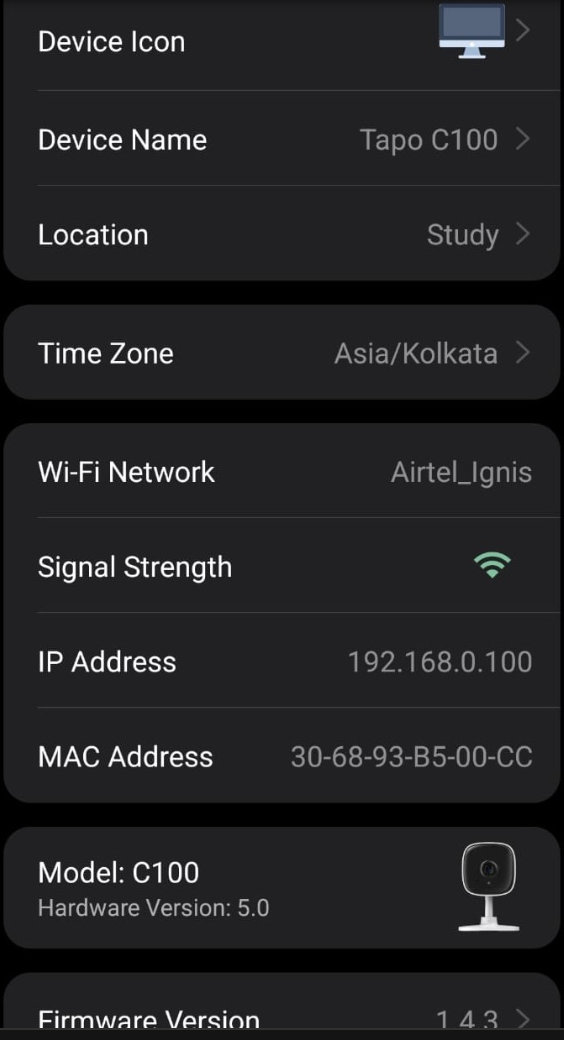
On the lab device, the camera IP was first identified using the Tapo mobile application
The attacker's exploit contains JSON parameters describing the target SSID, BSSID, password and encryption types. Since the service doesn't verify any authentication token, those JSON requests are accepted by the camera which could possibly -:
1. Result in a continuous Denial-of-Service attack.
2. Allow the attacker to intercept video/audio streams and use the camera as a foothold inside the victim's environment.
3. Elevates the issue beyond a simple DoS to a confidentiality compromise.
The following python exploit was used by us. The analogy is simple, supply a payload with the above parameters, disable SSL security including no certificate and hostname validation, and send it as an HTTPS POST request.

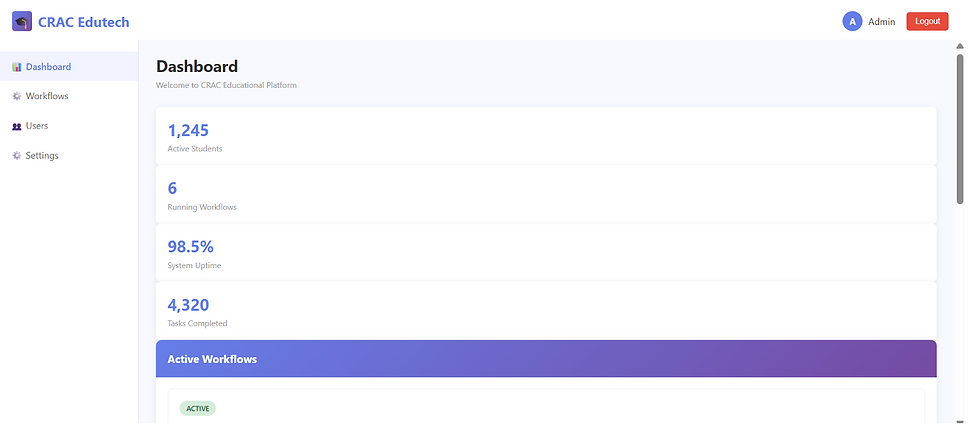
Upon sending the exploit to the camera, we got the following response and it connected successfully to the attacker controlled network.

The above script was used by us when we attempted a DoS attack on the camera. This automation script simply runs again and again, repeatedly triggering the Wi-Fi connection command from our exploit.
Proof of Concept
Detailed PoC Video can be found here -
How can this be fixed?
1. Enforce authentication on the connectAP endpoint before accepting any request.
2. Critical endpoints should be accessible only after secure pairing and not be exposed openly over the local network.
3. Implement validation and integrity checks on all incoming JSON parameters.
4. Add rate limiting and abuse protection on configuration endpoints.
We responsibly disclosed this bug to TP-Link on 18th February, 2026 and it was fixed on 4th April, 2026. TP-Link assigned us the CVE-2025-14300 that has a HIGH score of CVSSv4.0 8.7. It has the CWE-306 which is a 'Missing Authentication for Critical Function'.

![Top CRITICAL CVEs [9th March to 15th March, 2026]](https://static.wixstatic.com/media/fff29d_b4bb12f49e7647a284f2fd8462080ed6~mv2.jpg/v1/fill/w_980,h_1386,al_c,q_85,usm_0.66_1.00_0.01,enc_avif,quality_auto/fff29d_b4bb12f49e7647a284f2fd8462080ed6~mv2.jpg)
Comments