CRAC Insights — 9th Feb — 16th Feb
- CRAC Learning

- Feb 17
- 5 min read
Stay ahead of the curve with the latest from the CRAC Insights Newsletter! From critical zero-days to major infrastructure breaches, here is your quick briefing on the cybersecurity landscape:

TOP 3 CVES

CVE-2026–21531: Microsoft Azure SDK Remote Code Execution CVSS: 9.8 (Critical)
Affected Versions Microsoft Azure SDK components (vulnerable builds prior to the February 2026 security updates; organizations using unpatched SDK integrations are at risk).
Description A critical vulnerability in the Azure SDK allows attackers to exploit insecure handling of remote inputs and execute malicious code within affected environments. The flaw can be triggered through crafted requests or manipulated data flows interacting with vulnerable SDK components, potentially enabling unauthorized control over cloud workloads and applications.
Impact • Remote Code Execution on cloud services • Unauthorized access to sensitive resources • Privilege escalation within Azure environments • Data exfiltration and service disruption • Compromise of enterprise cloud applications
Mitigation • Apply Microsoft February 2026 security updates immediately • Upgrade Azure SDK to the latest patched version • Restrict external input sources interacting with SDK services • Implement strong access control and least-privilege policies • Monitor logs for unusual API activity or unexpected execution patterns
CVE-2026–0488: SAP CRM & S/4HANA Code Injection
CVSS: 9.9 (Critical)
Affected Versions
SAP CRM and SAP S/4HANA (Scripting Editor component) across multiple supported releases.
Description
A dangerous code injection vulnerability exists in SAP CRM and the Scripting Editor of SAP S/4HANA. An authenticated attacker with low-privilege access can exploit a flaw in a generic function module call to execute unauthorized actions including arbitrary SQL statements against the backend database.
Impact
• Complete database compromise, affecting confidentiality, integrity, and availability
• Unauthorized data access and modification
• Potential full application takeover and lateral movement within SAP landscapes
• Extremely high severity (CVSS 9.9) due to broad impact across ERP/CRM environments
Mitigation
• Apply SAP’s February 2026 security patches immediately
• Review and tighten user privileges for CRM and S/4HANA scripting access
• Monitor database activity for unexpected SQL execution
• Implement network segmentation to restrict access to SAP administrative interfaces
CVE-2026–21643: FortiClientEMS Critical SQL Injection CVSS: 9.8 (Critical)
Affected Versions FortiClientEMS version 7.4.4 (patched in 7.4.5).
Note: FortiClientEMS versions 7.2 and 8.0 are unaffected by this vulnerability.
Description A severe SQL injection flaw exists in the FortiClientEMS administrative interface. The vulnerability stems from improper neutralization of special elements in SQL commands, allowing an unauthenticated attacker to send crafted HTTP requests that are processed by the backend database.
Because no authentication or user interaction is required, an attacker can manipulate queries to execute arbitrary code or system commands directly on the vulnerable server.
Impact • Remote execution of unauthorized SQL and system commands • Complete compromise of the affected management server • Unauthorized access to sensitive data • Disruption of endpoint management operations • High potential for ransomware or lateral movement post-compromise
Mitigation • Apply the vendor’s security update and upgrade to FortiClientEMS 7.4.5 or later immediately • Restrict network access to the EMS administrative interface • Monitor web logs for unusual HTTP request patterns • Deploy web application firewalls to block SQL injection attempts
Top 3 News 9th Feb — 16th Feb

Cyberattack Shuts Down one of Europe’s biggest universities.
Since February 2, Sapienza University of Rome has been struggling to recover from a major cyberattack. For days, nobody could book exams, check tuition payments, or even look up contact info for professors. Most updates now show up on social media, but details are thin, and nobody knows when things will be back to normal.
The university said they pulled the plug on their network to keep the attack from spreading and to protect their data. It was a drastic move, but they didn’t have much choice. Officials aren’t sharing exactly what kind of attack hit them, but word is, it’s ransomware.
A lot of talk points to something called Bablock ransomware, possibly tied to a group that goes by Femwar02. One weird thing stands out: apparently, this malware skips over computers set up in Russian or other languages from former Soviet countries. It’s not proof, but it does make people wonder if there’s a Russian connection behind this attack.
Right now, Italian police and the National Cybersecurity Agency are digging into what happened. The university’s IT staff are still trying to figure out just how deep the damage goes and what backups can save. Nobody’s sure if they’ll get all the data back. Some of it might be gone for good.
For everyone at Sapienza, there’s just one thing on their mind: get everything working again, fast, and don’t let this ruin the school year. For cybersecurity folks, it’s one more sign that ransomware is getting smarter, and the good guys have to move even faster.
How an app abandoned by developers Stole 4,000+ Passwords
Researchers just uncovered something new and dangerous: the first case of a malicious Microsoft Outlook add-in stealing more than 4,000 user credentials. Here’s what happened. There was a popular add-in called AgreeTo, which worked just fine until its original developer walked away from it. Once the support and infrastructure expired, attackers swooped in. They took over the backend and swapped out the real content for a fake Microsoft login page.
Because Outlook add-ins can load web content from outside sources, the phishing page popped up right inside Outlook looking totally legit. People typed in their credentials, thinking everything was normal, while attackers quietly collected thousands of usernames and passwords.
This isn’t just about one add-in. It’s a bigger problem that’s baked into how software marketplaces work. Apps that businesses trust today can turn into security nightmares tomorrow if nobody’s keeping an eye on them. Abandoned tools, expired domains, and any add-in that pulls in content from the web, all of these open the door for attackers. It’s a reminder that trust in enterprise software isn’t a given; it has to be earned and maintained, or else users pay the price.
When Malware Starts Asking AI for Help
Cybercriminals aren’t just using AI to write better phishing emails; they’re hooking it right into live malware now.
Google’s Threat Intelligence Group just found that some attackers make real-time API calls to Gemini during their hacks. So instead of hiding all the bad stuff inside a file, the malware just grabs new code from AI while it’s running and uses it right away. There’s even a malware strain called HONESTCUE that’s already doing this.
So, why should you care? Because it makes spotting these attacks way tougher. Most security tools hunt for familiar patterns in malware. But when the code keeps changing on the fly, those patterns disappear.
Researchers also noticed hackers trying to dissect the AI itself. They’re firing off huge, structured prompts to figure out how Gemini works and maybe build their own versions.
Right now, AI doesn’t pull the trigger, it sharpens the aim, it helps them move faster when they’re poking around, writing code, or tricking people. It’s not taking over for humans yet, but it’s definitely speeding things up.
CRAC Events

Stop asking “Where to begin?” and start doing. 🚀
Join our Ethical Hacking Series for Beginners on Feb 21, 2026 which is targeted to make you industry ready and also train you for top certifications required in the field! We’re breaking down the basics of cybersecurity and giving away a CPENT Voucher to one deserving participant. Apply before 18 Feb, 2026.
🎟️How to join:
1️⃣ Save and this post.
2️⃣ Scan the QR code in the image.
3️⃣ Fill up the form to show interest and fill initial survey.
Selected Participants will be informed soon! Limited slots only.
Technical Deep dive

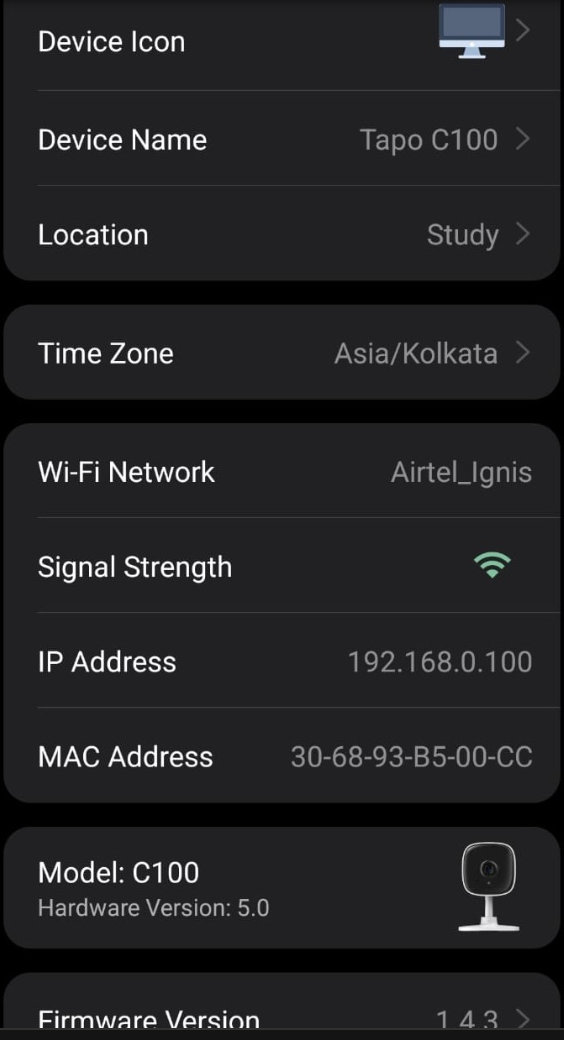
From Theory to Reality: CVE-2026–0918 Assigned! 🚀 The CRAC Learning team just leveled up. We’re thrilled to announce our first official CVE assignment as part of our impactful Smart Home Security research.
We discovered a vulnerability in Tapo C100 that allows an unauthenticated attacker to trigger a Denial of Service (DoS) via a NULL pointer dereference.
The result? A persistent crash loop that keeps the device offline.
Proud of the team Ayushman Agrawal Hingorani Azim Javed Praharsh Singh Kanishk Anand for turning curiosity into a tangible contribution to IoT security!
Meme of the Day



Comments