Smart Security Research Diaries: Attacking the Internet of Things
- Azim Javed

- Feb 10
- 4 min read
Before reading this part, go over our previous blog - https://www.crac-learning.com/post/smart-security-research-diaries-defending-the-internet-of-things

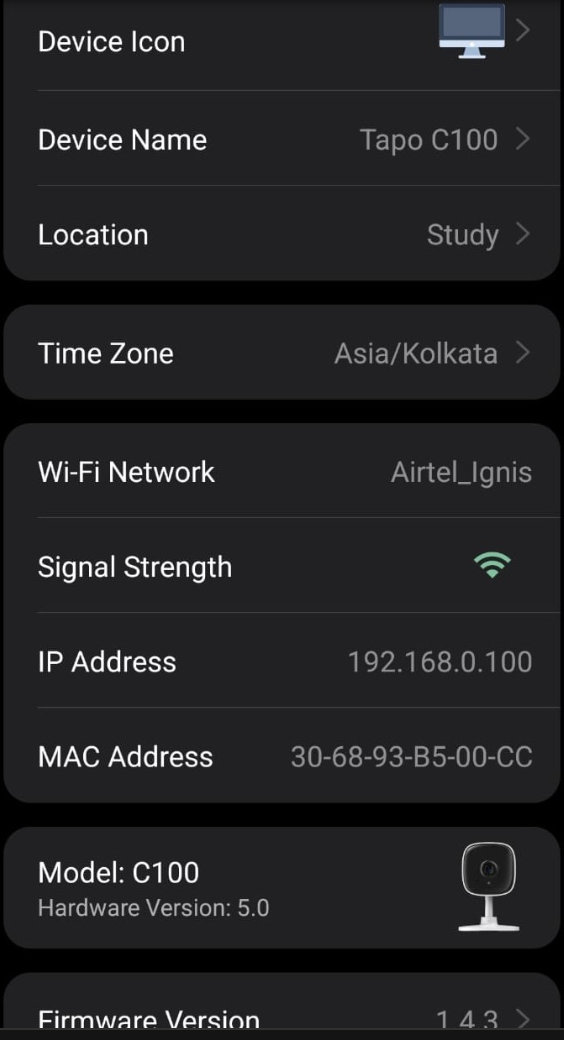
Then I started the Phase-1 of Smart Home Security Research Program by CRAC Learning with great enthusiasm & aspirations to find real vulnerabilities, not just solving TryHackMe labs. When I found that I'll be attacking the TP-Link Tapo C100 IP Camera, the first thing I did was Threat Modelling. I dived deep into gathering past vulnerabilities and CVEs given to the Tapo C200 and C210 IP cameras as these two were suggested by my mentors for the program. I thank ChatGPT's Web search feature. It literally saved me tens of hours. With this feature, I was able to collect almost all the information about past vulnerabilities and CVEs assigned to the targets in not more than 3 hours. I divided the vulnerabilities into the following categories-
1. Network-Level Denial-of-Service Attacks
2. Authentication and Authorisation Failures
3. Remote Code Execution Vulnerabilities
4. Cryptographic and Credential Management Weaknesses
5. Physical Access Vulnerabilities
I analysed the weak points and potential attack surfaces of the target which could be tested to exploit successfully. I concluded that many high-impact vulnerabilities required only local access rather than direct exposure on the internet, which challenges the assumption that IoT devices are safe if they are not publicly accessible.
I documented all this information formally in an IEEE style-paper and I thank myself for doing so because it really helped me and my team a lot in the later stages of the program to check back the threat model for ease.
Finally, the information gathering and reconnaissance stage came to an end and it was time to finally penetrate into the Tapo C100. The team planned an offline meeting at Connaught Place, New Delhi. It was really nice to be meeting my team for the first time in-person. My mentor Ayushman Agrawal Hingorani Sir, came along with the Hardware— the IP Camera, a router, and some other miscellaneous items. I opened a wifi router for the very first time. It was pressure packed and I got a small cut on my thumb while opening it (I guess it's very normal for newbies!). Unfortunately, the router didn't have any debug ports and we were out of fancy equipment to extract the firmware from it. Also, performing advanced side-channel attacks was out of scope for this particular program as all of us didn't even have the basic knowledge of hardware pentesting (except the mentor obviously!). So we had to drop out the wifi router and then came the final target. We started pentesting the camera directly as we had almost all the information (thanks to the paper!). I used Nmap to find all the services being used/offered by the camera which were https, rtsp, xinupageserver, https-alt and sunwebadmin. I was a bit overjoyed and even shocked that we were able to successfully find a "HIGH" severity Buffer-Overflow based Denial-of-Service vulnerability on the very first day. The technical details can't be disclosed now as I'm still in communication with the security team. A CVE will be shortly assigned to us regarding this vulnerability as it has been acknowledged by TP-Link. We ended the day with some burgers and coke! (oh come on, it was a well-deserved treat)
The next week we had another offline meeting, this time in Gurugram. The day started with some network troubleshooting and system administration as we forgot to bring our wifi router that was earlier acting as a gateway. But yeah, after scratching our heads we were finally able to use one of our laptops as the gateway which really helped us capture all the data frames via Wireshark. This time we tried to expand our horizon and tried to find out some Remote Code Execution vulnerabilities. By again using the threat model, I played with various API endpoints including CreateRules and ModifyRules but everytime, I got the same output {"error_code":-40209} which was extremely unusual. After reading the documentation from official sources, I realised that the bug which I was trying to replicate had already been patched. Therefore, I jumped onto another vulnerability which was about injecting a reverse payload in the camera's uhttpd server. The server didn't have any input fields so I dropped this plan as well. After around 5-6 hours of grinding and almost a burnout, we concluded that, "KNOWING WHAT DOES NOT WORK IS AS EQUALLY IMPORTANT AS KNOWING WHAT DOES!". Because of this, we ended up with a positive vibe and more enthusiasm to work on the targets.
In the next offline meetings, our mentor got some Cisco switches and routers. It was supposed to be a learning day! We learned about core networking concepts and did hands-on with the routers and switches. That day was also truly valuable, it made me realise how idiot I am!
In the most recent session, I was able to exploit another "HIGH" severity vulnerability resulting in complete disconnection of the camera from its primary wifi to an attacker controlled wifi giving us complete control of the camera. Again, due to Ethical Vulnerability Disclosure policies, I can't dive in the technical details as the communication with TP-Link's Security team is still ongoing.
Finally, the Phase-1 came to an end where we were successful in finding two "HIGH" severity vulnerabilities over 4 weeks with just 4 offline meetings. However, I'll appreciate my team members and myself that we dedicated a lot of time in researching and scratching our heads at our homes. The Phase-1 alone made me learn way more than any TryHackMe lab could ever possibly do. Seriously, just one month with an amazing team has boosted my confidence to the peak level and I plan to continue with this enthusiasm in the coming months. We are planning to purchase some other hardware tools and maybe a new target this time so that we can dive deep even into the Hardware section this time. Let's see what all we can hack in the coming months! (ethically, of course!)

Comments