Stop Hunting Bugs & Start Hunting Chains (based on Ni8mare)
- Om Mishra

- Mar 6
- 4 min read

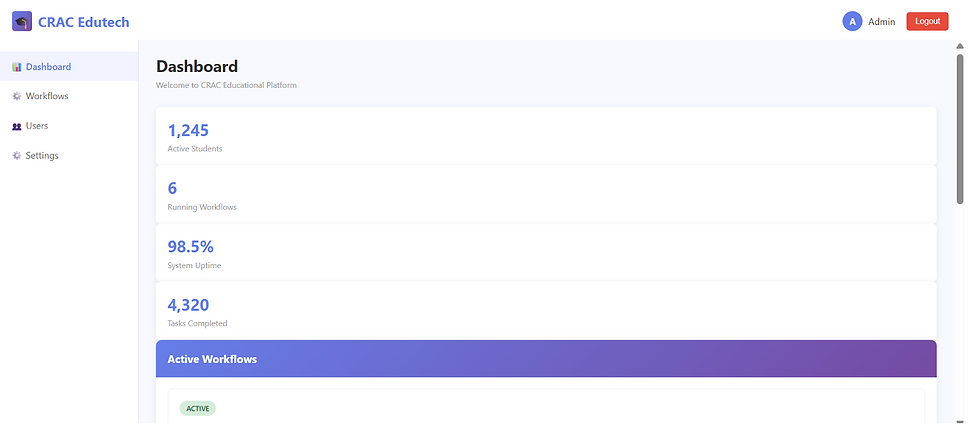
This blog explores vulnerability chaining using an n8n Ni8mare-inspired attack path to demonstrate how seemingly harmless weaknesses can compound into something catastrophic. Let’s start with a hard truth. Most security programs are optimized for counting bugs not understanding compromise. We rank vulnerabilities by CVSS. We prioritize the red ones & close tickets. We feel productive but attackers don’t think in scores. They think in sequences. They don’t ask Is this bug critical? They ask What does this become when I combine it?
Individually they are fixable. But together? Catastrophic. This isn’t just a vulnerability write-up. This is a demonstration of how compromise actually happens.
The Conceptual Foundation: Attack Surface vs. Attack Path
There are two ways to look at security: Attack Surface View: How many vulnerabilities do we have? & Attack Path View: If I were an attacker, how would I move from nothing to root? The Ni8mare Chain is an attack path. It transforms: Unauthenticated internet user → Authenticated admin → Secret holder → Identity forger → OS-level command executor
Before moving on to the POC lets us first understand the vulnerabilities present in the app through its code.
Weak Secret Management: The Foundation of Token Forgery

SECRET_KEY = n8n-default-secret
What’s Happening: The application uses a hardcoded, predictable secret key for signing tokens.
Why This Is Dangerous
This violates core cryptographic principles:
· Secret is embedded in source
· No rotation strategy
· Same value across environments
· Looks like a default placeholder
If the source code leaks (GitHub exposure, backup leak, CI logs), the secret is permanently compromised.
Secrets must be:
· Unique per environment
· Stored in secure vaults
· Rotated regularly
· Never committed to source
Without this, cryptography becomes decorative.
Chain Impact
An attacker who knows the secret can:
· Recreate valid HMAC signatures
· Forge arbitrary tokens
· Maintain long-term persistent access
This becomes the persistence layer of the attack chain.
Broken Authentication: Base64 Is Not Security

What’s Happening
The system checks whether the cookie:
· Can be base64 decoded
· Produces valid JSON
If yes then user is authenticated.
What’s Missing
· No signature validation
· No HMAC verification
· No expiration check
· No role validation
· No integrity protection
This is not authentication. It’s parsing.
Security Concept: Authentication vs Parsing
Authentication means: Can we verify this identity cryptographically? This code asks: Does this look like JSON? Those are not the same thing.
Chain Impact
An attacker can:
1. Create JSON:
2. {"username": "attacker", "role": "admin"}
3. Base64 encode it
4. Set it as admin_token
Instant privilege escalation. No brute force needed.
Content-Type Confusion: Conditional Trust Collapse

if 'files' in request.form or 'files' in request.files:
is_admin = True
else:
is_admin = is_authenticated()
What’s Happening
Authentication logic changes based on how the request is parsed. If the request contains a file-like object → bypass authentication.
Parser Differential / Content-Type Confusion
Different request formats produce different parsing results:
· application/json
· multipart/form-data
· application/x-www-form-urlencoded
If authentication depends on parsing behavior, attackers can manipulate Content-Type headers to influence trust decisions. This breaks the trust boundary.
Chain Impact
This becomes the entry point. No token forging needed. Just send a crafted multipart request → instant admin.
Command Injection: Remote Code Execution
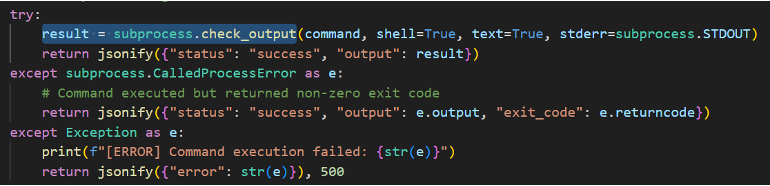
result = subprocess.check_output(
command,
shell=True,
text=True,
stderr=subprocess.STDOUT
)
What’s Happening
User input is passed directly into a shell command. With shell=True, special operators become active:
;
&&
|
>
$()
Injection via Shell Invocation
When you use shell=True, you are giving the user access to:
· The shell interpreter
· Command chaining
· File redirection
· Subshell execution
This is direct OS-level exposure.
Chain Impact
Once authentication is bypassed:
· Full remote code execution
· Data exfiltration
· Reverse shell deployment
· Lateral movement
· Persistence installation
This is the final stage of the chain.
Direct Database File Exposure: Intelligence Amplifier


return send_file(DB_PATH, mimetype='application/octet-stream')
With a bypass header:
if request.headers.get('X-Bypass') == 'files':
What’s Happening
The raw SQLite database file is served directly.
Insecure Direct Object Exposure
Databases are not API responses.
Serving raw storage artifacts exposes:
· User credentials
· Roles
· Secrets
· Business logic data
There is no access control enforcement.
Chain Impact
The attacker gains:
· Passwords (stored in plaintext)
· User roles
· Workflow logic
· Internal metadata
This enables reconnaissance and escalation refinement.
Token Forging Endpoint: Privilege Escalation as a Service

@app.route('/api/forge-token')
This endpoint literally generates admin tokens.
Critical Issues
· Static secret reused
· 365-day expiration
· No token ID (jti)
· No issuer validation
· Returns unsigned token variant
Broken Cryptographic Design
Tokens require:
· Signature validation
· Expiration enforcement
· Revocation tracking
· Context validation (issuer, audience)
This endpoint turns privilege escalation into an API feature.
Chain Impact
Even without DB extraction:
· Anyone can mint admin tokens
· No revocation possible
· Persistent admin access
Version Disclosure: Reconnaissance Enabler

version": "1.0.0-vulnerable
Why This Matters
Version leaks:
· Confirm exploit compatibility
· Reduce attacker guesswork
· Increase precision
Alone? Low severity. But in a chain? High value.
Weak Database Initialisation: Credential Collapse

c.execute("INSERT INTO users VALUES (1, 'admin', 'admin123', 'admin', 1)")
Problems
· Plaintext password
· Weak password
· No hashing
· No salting
Security Concept: Credential Hygiene Failure
Passwords must be:
· Hashed (bcrypt/argon2)
· Salted
· Rate limited
· Never default weak values
Chain Impact
If the DB is downloaded: Instant admin compromise
Password reuse risk across systems

Comments